Ask any security manager how they would deal with the threat of Unmanned Aerial Vehicles, more commonly known as drones, and the conversation will probably turn to counter measures and the need to knock the drone out in flight, either by signal jamming, electronic “sky fencing” or net guns and impact munitions.
While all options are feasible, most, if not all, are illegal in the UK and for the most part can only be implemented by government agencies under strict authorisations. Eclipse Digital Solutions advocates a three-step approach: Detection, protection and reaction.
Detection
An airspace incursion audit should be the first step in your risk mitigation plan.
Long range radio frequency (RF) scanners assisted by intelligent software and reporting tools can, over a period of around 30 days, give a detailed view of the risks you face.
Once you understand your airspace incursion risk, you can move to stage two.
Risk protection and airspace awareness
An enhanced version of step one but with more emphasis placed on understanding the UAVs in your airspace and capturing forensic data, along with giving a high-profile view of your action plan.
Businesses with little or no risk may wish to simply continue with random airspace audits and publicise their actions to act as a deterrent.
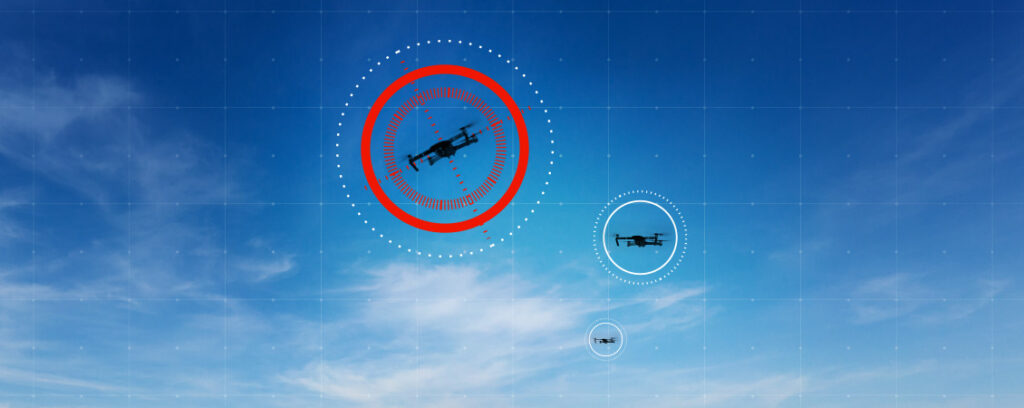
Those with a greater risk variant may seek to plan for more frequent surveillance and auditing or consider installing their own permanent system, leveraging the RF detection capabilities with video analytics to give the best possible detection and warning of airspace threats.
Software integration can drive many security countermeasures and smart building integrations giving you the option to automatically trigger defensive actions.
Reaction plans
Reacting to a drone threat depends on many factors including your own risk approach, vulnerability and threat level to name. In most cases, your action plan will combine both active and passive protocols.
Passive actions can almost always be driven by software integration with security architecture that allows semi or fully automated response and reaction to threats. Simple lockdown, network isolation or shutdown, visibility interruption or cloaking can all be triggered and immediate alerts sent via email, SMS or onscreen control room notifications.
For active measures, it’s preferable to have physical intervention plans that ensure a guard force or employee plan to view the UAV to verify the extent of the threat.
Options to trace the drone pilot’s location can be deployed either via enhanced RF and video triangulation, or by static observation should the pilot be operating in line of sight of the drone.
Emergency service liaison is important too. They should be made aware that a response to an incursion incident is planned for and understand the actions you intend to take.
Many drones can be traced via MAC address and serial numbers and in most cases this data can be captured from a drone whilst being tracked in flight.
Eclipse’s drone detection and mitigation systems can protect your perimeters by identifying and deterring unwanted drones. For more details call us on 0370 760 5600.